Proactive Detection in Action: How MaxiCyber Stopped a SharePoint Exploit Before Microsoft’s Disclosure
Summary
At MaxiCyber by Maximum Group Digital, proactive threat detection isn’t just a feature — it’s the foundation of how we protect organizations. In this post, we break down a critical Microsoft SharePoint vulnerability that was actively exploited in the wild — and how our systems detected and blocked it weeks before Microsoft publicly disclosed the flaw on July 8, 2025.
By identifying malicious activity targeting SharePoint endpoints such as /_layouts/15/toolpane.aspx, MaxiCyber successfully mitigated the threat as early as May 2025, shielding our clients long before a CVE, patch, or public advisory existed. This real-world case demonstrates the power of proactive, intelligence-driven cybersecurity.
Understanding the SharePoint Exploit
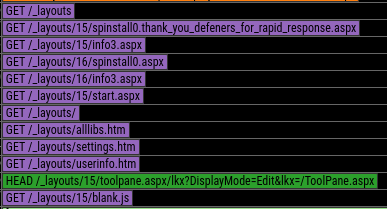
The exploit we observed in early 2025 targeted Microsoft SharePoint’s internal page handling mechanisms — specifically components within the /_layouts/ virtual directory, including toolpane.aspx.
These endpoints are core to SharePoint’s internal architecture, enabling administrators and site editors to manage web parts, personalization settings, and page configurations. However, under certain conditions, attackers were able to abuse these internal pages to escalate privileges without proper authentication.
Key Targeted Endpoints
- /_layouts/15/toolpane.aspx
- Other internal _layouts endpoints related to personalization and user context
Although these pages are intended for legitimate administrative use, the vulnerability allowed attackers to manipulate how SharePoint handled user context, permission inheritance, and rendering logic, opening the door to unauthorized privilege escalation.
Why This Exploit Was Especially Dangerous
This vulnerability posed a high-risk threat due to several factors:
- No user interaction required — attackers could send malicious requests directly to vulnerable endpoints.
- Abuse of legitimate SharePoint functionality, making the activity difficult to detect using traditional signature-based tools.
- Token manipulation or access control weaknesses, enabling impersonation of privileged users.
- Public exposure risk — in many environments, /_layouts/toolpane.aspx was publicly accessible due to legacy configurations or perimeter misconfigurations.
Together, these factors created a stealthy and scalable attack vector capable of bypassing conventional defenses.
Timeline: Exploitation Attempts Before and After Disclosure
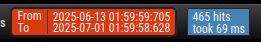
MaxiCyber’s telemetry detected targeted exploitation attempts as early as May 2025, indicating sophisticated, limited-scope activity likely conducted by advanced threat actors.
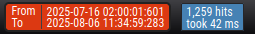
By June and July 2025, we observed:
- Increased scanning activity
- Higher exploitation volume
- A sharp spike immediately after July 8, 2025 — the date Microsoft publicly disclosed the vulnerability
Activity in May 2025


Activity in June 2025

Activity in July 2025

The image below shows the malicious requests of this exploit.
This timeline reinforces a critical reality: attackers often exploit vulnerabilities long before public advisories exist.
How MaxiCyber Detected and Blocked the Threat Early
Unlike traditional reactive security tools, MaxiCyber relies on:
- Behavioral analytics
- Custom detection logic
- Threat pattern correlation
- Continuous telemetry monitoring across protected environments
This allowed us to identify anomalous SharePoint request behavior in May 2025, classify it as malicious, and automatically deploy mitigation measures — without waiting for vendor confirmation, CVE assignment, or public patch releases.
The Result:
- All MaxiCyber clients were protected
- No data breaches
- No successful exploitation
- No operational impact
The threat was neutralized before it could escalate.
Why Proactive Defense Is the Future of Cybersecurity
This incident highlights a growing truth in cybersecurity:
Waiting for public advisories is no longer enough.
Threat actors move faster than vendors, CVE databases, and patch cycles. Organizations relying solely on signature-based detection or reactive response models will always be one step behind.
Proactive, intelligence-driven defense — detecting suspicious behavior before it becomes public knowledge — is the only sustainable way to stay ahead of modern threats.
At MaxiCyber, we don’t just respond to known risks.
We discover, detect, and stop threats before they’re known.
Protect Your Organization with MaxiCyber
If you want cybersecurity that predicts threats instead of reacting to them, MaxiCyber is built for that mission.
🔗 Learn more about MaxiCyber:
https://maximumgroupdigital.co.za/platforms/maxicyber/